What Is Ethical Hacking and How Ethical Hackers Prevent Attacks

Reading Time: 14 minutesTable of Contents Introduction Cyber attacks can damage businesses, expose sensitive data, and disrupt networks within minutes. Have you ever wondered what ethical hacking is and why organisations depend on ethical hackers to secure their systems? Ethical hackers identify vulnerabilities before cybercriminals can misuse them, helping companies improve overall protection and reduce risks. This blog […]
How to Master Data Science with Python from Beginner to Pro?
Reading Time: 14 minutesTable of Contents Introduction How can you transform raw, messy data into meaningful insights using data science with Python, even if you are starting from zero? Most beginners struggle at the beginning of their journey because they try to learn everything at once—machine learning, libraries, statistics, and coding—without a proper structure. This leads to confusion […]
Exploring Types of Ethical Hackers and Their Importance in Threat Prevention

Reading Time: 18 minutesTable of Contents Introduction Struggling to keep up with rising cyberattacks that silently expose your business to risk? Cyber threats are growing faster than most organisations can handle, leading to unexpected data breaches, costly ransomware attacks, and hidden network vulnerabilities. Many businesses realise the danger only after damage is done, simply because they lack clarity […]
Which Cybersecurity Courses After BSc Create the Best Path to High-Demand Jobs?

Reading Time: 18 minutesTable of Contents Introduction Finished your BSc and wondering how to step into a high-growth IT career? Cybersecurity is one of the most in-demand fields today, offering exciting job roles, strong salary potential, and rapid career advancement for graduates with the right skills. Choosing the right Cybersecurity courses after a BSc can open doors to […]
10 Powerful Ethical Hacking Techniques Every Cybersecurity Beginner Should Know

Reading Time: 15 minutesTable of Contents Introduction Cyber attacks have increased by more than 300% in recent years, yet many organisations still struggle to find professionals who think like attackers. If you are serious about cybersecurity, reading about threats is not enough. You must understand the exact ethical hacking techniques that security professionals use to uncover vulnerabilities before […]
API Security Testing Explained with a Step-by-Step Approach for Beginners

Reading Time: 14 minutesTable of Contents Introduction In today’s interconnected digital ecosystem, API security testing has become a critical skill for anyone entering networking or cybersecurity. APIs silently power mobile apps, cloud platforms, and enterprise systems, yet they are often the weakest link in network security. Beginners frequently struggle with unclear guides that focus on theory but skip […]
What Is the Difference Between IPv4 vs IPv6 Addressing?
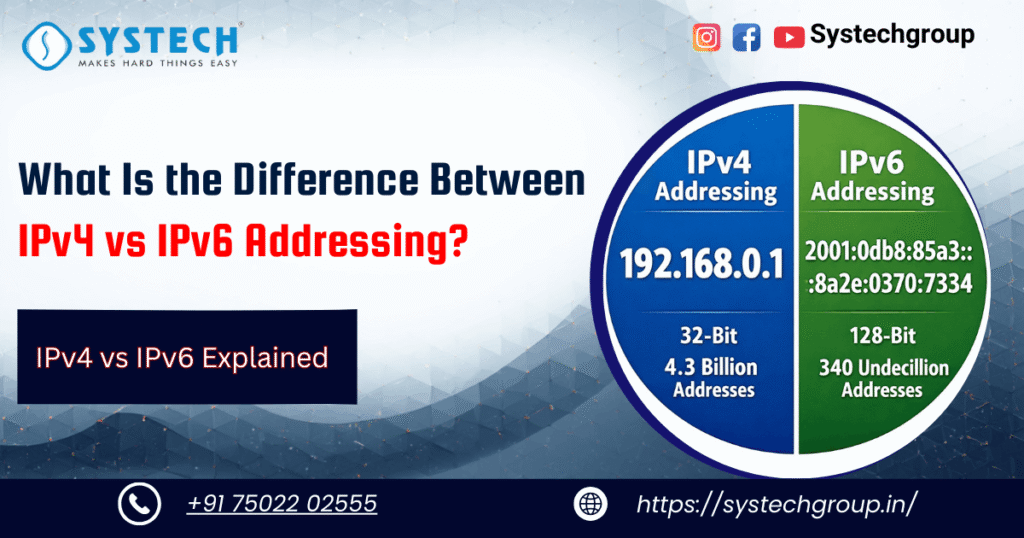
Reading Time: 15 minutesTable of Contents Introduction: New to networking? IP address problems can slow you down quickly. Devices fight for a limited address space, labs stop working, and troubleshooting becomes confusing. This is where understanding IPv4 vs IPv6 addressing makes a real difference. IPv4 is old and running out of space, while IPv6 is new and practically […]
Top 5 Essential Factors to Consider Before Paying the Cost of the CCNP Certification Course in Chennai

Reading Time: 14 minutesTable of Contents Introduction: In the fast-evolving IT and networking industry, having advanced certifications is no longer optional—it’s essential. The Cost of the CCNP Certification Course in Chennai often raises questions among aspirants: Is the investment worth it? Will it genuinely enhance career prospects, or is it just another expense? Many networking professionals in Chennai […]
Why Cybersecurity Professionals Are the Backbone of Modern Business

Reading Time: 13 minutesTable of Contents Why Cybersecurity Professionals Matter in Today’s World In today’s hyper-connected world, businesses of every scale rely heavily on digital platforms for operations, transactions, and communication. But this dependence on technology also exposes companies to a rising wave of threats like data breaches, ransomware attacks, and insider risks. The ones standing guard against […]
How to Master Subnetting for CCNA and Networking Success

Reading Time: 11 minutesTable of Contents Introduction Networking can feel overwhelming when you first start preparing for CCNA or other certifications. One of the biggest challenges students face is understanding subnetting. Without solid subnetting skills, you may struggle with IP addressing, routing, and even real-world troubleshooting. The good news is that subnetting is not as scary as it […]
